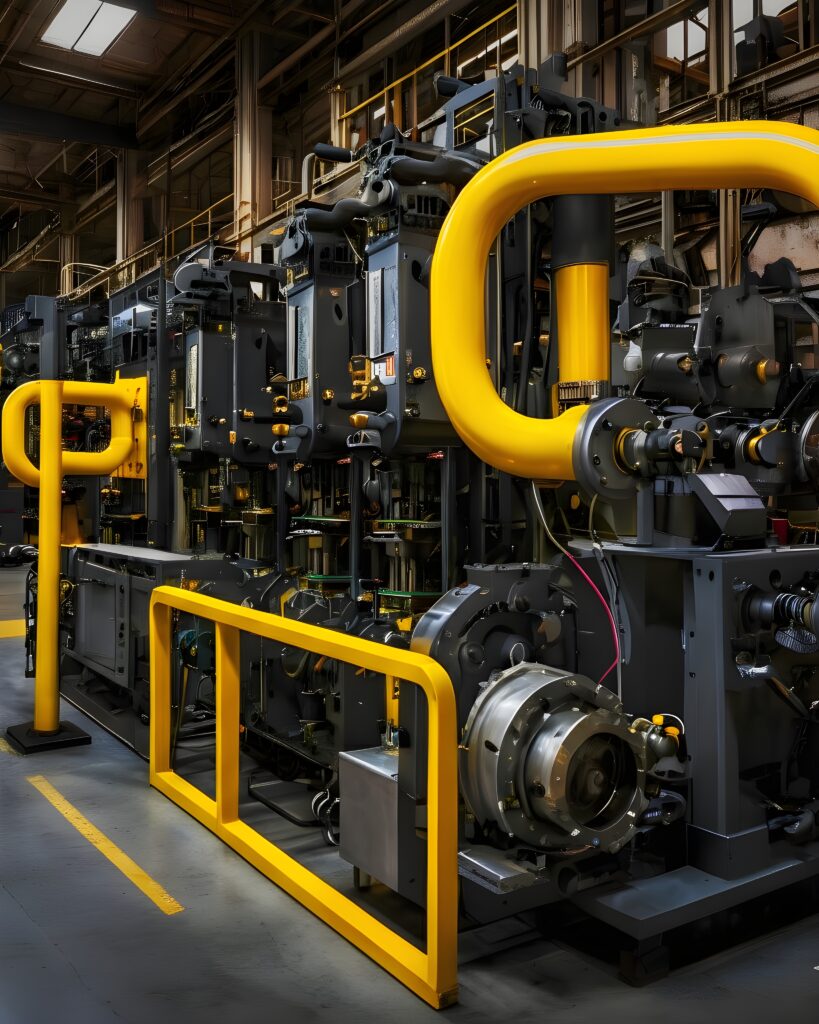
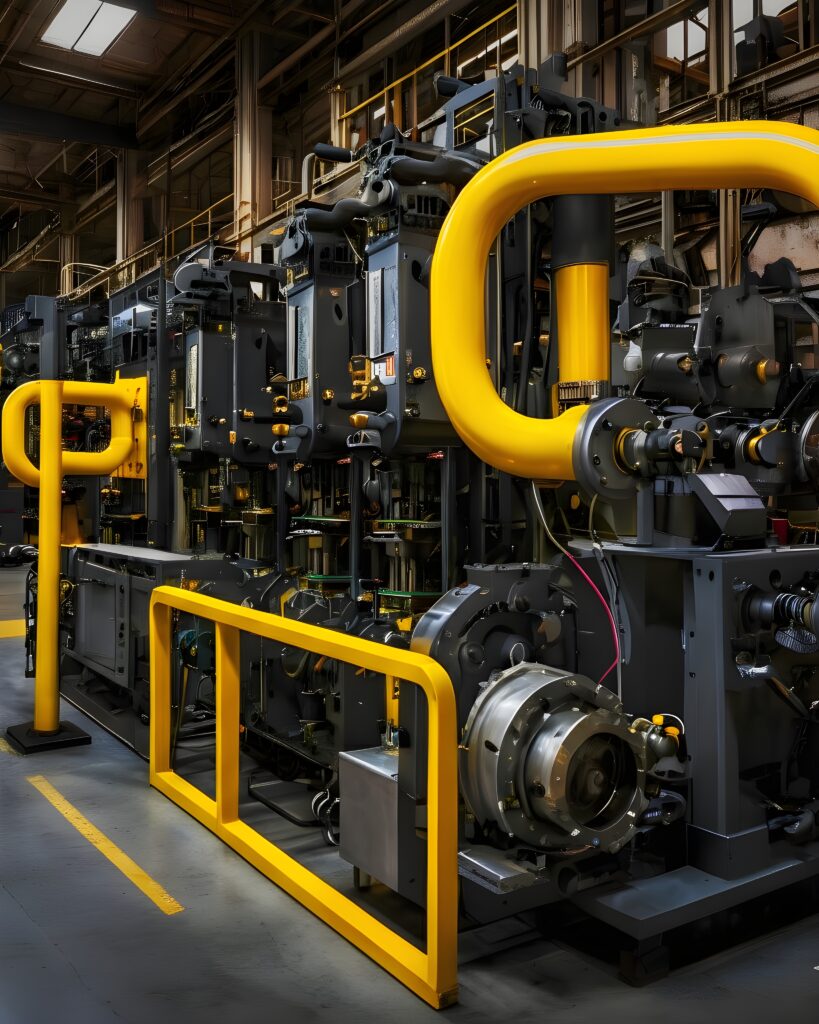
Your industrial and critical infrastructure systems are too important to leave unsecured. Operational Technology (OT) and Industrial Control Systems (ICS) power the backbone of critical infrastructure. From electricity grids and water treatment plants, to manufacturing, oil and gas, and transportation networks.
Increasingly, attackers are targeting OT networks with ransomware, sabotage, and data exfiltration.
OT networks are highly sensitive, often fragile, and run legacy devices. A single aggressive scan or misconfigured test can disrupt operations within minutes, potentially impacting safety, production, and revenue.
Our Operational Technology (OT) and Industrial Control Systems (ICS) Security Testing finds vulnerabilities safely. We provide actionable remediation, keeping your operations, personnel, and assets protected.
What we offer
To strengthen your industrial and critical infrastructure, contact us for our Operational Technology (OT) and Industrial Control Systems (ICS) Security Testing.
Identification without disruption
Our Operational Technology (OT) and Industrial Control Systems (ICS) Security Testing identifies exploitable weaknesses without disrupting operations.
Methodological approach and simulation
We use a careful, methodical approach and draw on more than 10 years of hands-on experience. We work closely with OT engineers to identify weaknesses and simulate real-world attacker behaviour, where possible, while keeping your operations safe.
Outcomes
You will gain actionable insights to strengthen your defensive posture and mitigate risk to your systems.
What you receive
Our Operational Technology (OT) and Industrial Control Systems (ICS) Security Testing will give you a clear understanding of how attackers could exploit your infrastructure, and how to prevent this from happening.
We create a comprehensive and actionable report, which includes:
A summary highlighting operational risk
Technical findings for each device and network segment
Safe, proof-of-concept demonstration of successful attacks
Remediation guidance based on operational impact
Recommendations for improving security for your IT and OT teams
industries
Who we’ve helped
Our team has extensive experience across key critical infrastructure and industrial sectors, including:
Electricity and Power Generation
Water and Wastewater Management
Manufacturing
Oil and Gas
Transportation
Your organisation’s attack surface is unique. Our approach will suit the specific technologies, infrastructure, and risk profile of your environment.
What we assess
Our Operational Technology (OT) and Industrial Control Systems (ICS) Security Testing looks at the full operational technology stack. We’ll give you examples of any vulnerabilities we uncover. A real-world scenario is a single compromised account leading to an attacker taking full operational control – manipulating processes or halting production. We can see the importance of account hygiene, monitoring, and segregation of duties.
We evaluate network design, firewalls, VLANs, and IT-OT boundaries. Vulnerabilities include flat networks allowing lateral movement from IT to OT, insecure VPNs and remote access points, firewall rules for critical systems, inadequate monitoring and alerting.
Weak account management is a major risk in OT environments. Insecure accounts are common. Vulnerabilities include shared operator or service accounts, accounts with excessive privileges, IT users with inappropriate OT access, defunct accounts, weak passwords or missing MFA, poor separation of duties between IT, OT, and operational staff, remote vendor accounts with unnecessary access.
We assess network segmentation, protocol security, and device communications. Vulnerabilities include exposed SCADA services on the network, weak credentials on PLCs and HMIs, insecure protocol traffic and remote access to control systems.
We examine firmware, protocols, and physical interfaces for potential compromise points. Vulnerabilities include insecure passwords, firmware vulnerabilities, insecure serial or network interfaces.
We test authentication, session management, and backend interactions. Vulnerabilities include weak HMI authentication, misconfigured access to control functions, potential for operator command spoofing.
We assess how critical operational data is protected and whether process integrity can be maintained under attack scenarios. Vulnerabilities include manipulation of sensor data, unauthorised changes to PLC or HMI logic, unsecured historian databases, inadequate logging and audit trails.
What frameworks we follow
Our Operational Technology (OT) and Industrial Control Systems (ICS) Security Testing aligns with global and regional standards. This ensures compliance and best practices for critical infrastructure security:
ISA/IEC 62443
NIST SP 800-82
NZISM
ISO/IEC 27001
NERC-CIP
IEC 42553
Regional guidelines such as the ASD Essential Eight inform configuration and hardening recommendations. They are not a primary OT penetration testing methodology, however.
FAQ
Find answers to common questions about our services and what to expect from your experience with us.
Will testing disrupt operations?
No. All testing is conducted safely, with OT engineer oversight and operational safeguards.
Do you test legacy ICS/OT systems?
Yes, including PLCs, SCADA, HMIs, and network infrastructure.
Can remote OT access be assessed?
Yes, we evaluate VPNs, remote operator access, and cloud-connected OT systems.
How often should OT/ICS testing be performed?
Typically annually, or after major system changes or new device deployment.

Let’s work together
Ready to enhance the security of your industrial and critical infrastructure systems?
You’re in the right place.