Realistic Scenario: How One Click Becomes a Tenant Breach
A low-privileged user falls for a phishing email and enters credentials on a spoofed Microsoft login page.
- No MFA is enforced. Conditional Access? Not configured.
- The attacker logs in via IMAP, which bypasses modern MFA.
- Inside the mailbox, they find sensitive internal threads and add a transport rule to forward all messages to an external account.
- A calendar invite links to a shared Teams channel. The attacker uses it to access a document library – and finds internal PII on SharePoint.
- All from one compromised account in a poorly configured Microsoft 365 tenant.
Intro: The illusion of security
Many organizations believe Microsoft 365 is secure by default. It’s Microsoft, after all – surely it handles security?
That confidence is misplaced.
Microsoft 365 operates under a shared responsibility model : Microsoft secures the infrastructure, but you are responsible for your data, identities, access controls, and configuration. And most tenants we’ve reviewed recently? They’re not configured for real-world threats.
This post is not a checklist. It’s not compliance talk.
It’s an offensive look at what attackers can do once they’re in – and how common M365 misconfigurations give them everything they need.
Microsoft 365: Shared Responsibility Model
Before we dive into offensive techniques, let’s set the foundation.
Here’s a simplified view you can use with stakeholders or leadership:
Microsoft’s Responsibility
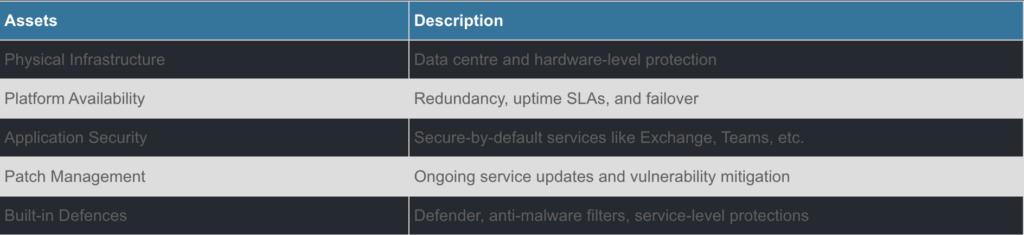
Your organisations responsibility:
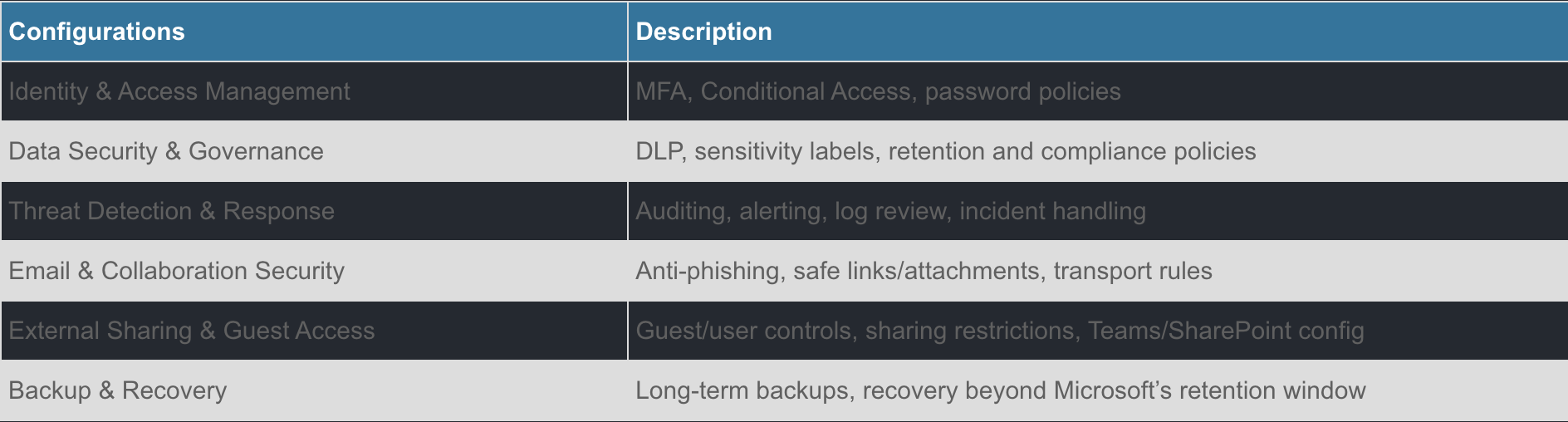
Bottom line: Microsoft gives you the tools. It’s your job to use them.
How attackers abuse misconfigured M365 tenants
Here are the most common weak configurations we’ve seen – and how they can be weaponized.
Global Admins Everywhere
Too many organizations assign global admin roles to service accounts or shared mailboxes. Once an attacker compromises any of those accounts, it’s game over – full control of the tenant without lifting another finger.
TTP: Token theft or password spraying against shared mailboxes or app registrations → Admin token reuse across services like Graph API or Exchange.
Real-World Example: The Storm-0558 attack involved stolen tokens that granted wide access via misconfigured apps and keys. Privileged accounts made it worse.
Legacy Auth + No Conditional Access
Still supporting legacy authentication? No Conditional Access policy? Perfect. Attackers can brute-force, spray, or replay creds via protocols like IMAP or SMTP AUTH — all of which bypass MFA.
Attackers can add forwarding rules to external mailboxes without raising alerts if policies are too relaxed.
TTPs: Password spray via IMAP or EWS → no MFA challenge → mailbox access → create hidden inbox rules → persistence + data exfil.
Over-Permissive Guest Access
M365 tenants love external collaboration. But when guests are poorly managed, attackers can gain access to conduct lateral movement within the tenant or exfiltrate sensitive data through unmonitored or unrestricted access channels.
TTPs: Use a compromised guest account to pivot via Teams channels, shared docs, or guest directory enumeration.
Real-world Example: In the SolarWinds campaign, lateral movement and privilege escalation happened via cloud identities and OAuth abuse across tenants.
Exchange Transport Rules: The Covert Exfil
Many tenants have mail transport rules that whitelist trusted domains. If an attacker either controls or compromises the trusted domain, they can silently forward internal sensitive email to that domain without detection.
TTPs: Create forwarding rule + auto-delete on inbox = quiet data leak
Safe Attachments & Malware Notifications Off
No Safe Attachments? No malware alerts? One ZIP and you’re done.
Users can even install malicious Outlook add-ins.
TTPs: Use obfuscated Office macros, malicious add-ins, or zipped payloads to bypass relaxed attachment filters. Outlook add-ins or OAuth apps grant silent, persistent access.
Mapping: Misconfigurations → Attacker objectives
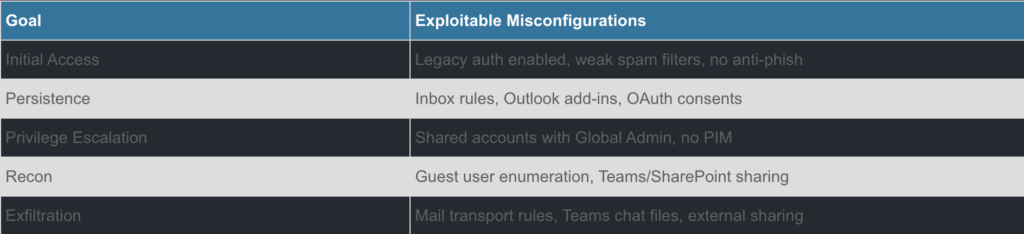
Assume Breach: Why default isn’t secure
Most attackers don’t hack in . They log in .The real risk isn’t the initial compromise – it’s how easy it is to move laterally and persist in a misconfigured tenant.
Helpful Microsoft resources
- Microsoft 365 Security Best Practices: Read HERE
- Microsoft Shared Responsibility Model: Read HERE
- Defend against threats with Microsoft 365 – Training: Read HERE
Final Thoughts: Secure by design, not by default
Microsoft 365 is powerful, flexible, and dangerously forgiving.
This isn’t about blaming sys admins or security teams. It’s about recognising that cloud misconfigurations are the new perimeter, and attackers are already counting on you to miss a few switches.

Let’s Connect!
Ready to Take the First Step Toward Cyber Security transformation?
You’re in the right place.