Our Security Configuration Reviews help organisations ensure that their infrastructure, cloud platforms, and enterprise applications are securely configured and aligned with best practices.
Even well-secured environments can contain configuration weaknesses that expose systems to attackers.
Modern enterprise environments are complex systems. They include endpoints, servers, network infrastructure, cloud platforms, and Software as a Service (SaaS) applications. Misconfigurations are one of the most common causes of security breaches.
By reviewing system configurations across multiple technologies, we help organisations reduce their attack surface and prevent exploitation before attackers can take advantage of misconfigured systems.
What we offer
Contact us for a Security Configuration Review, and to strengthen your security posture.
Security configuration review service
Attackers frequently exploit misconfigurations rather than sophisticated vulnerabilities because they are easier to identify and often provide direct access to sensitive systems.
Our Security Configuration Review service evaluates the security of your infrastructure. We’ll identify configuration weaknesses, insecure defaults, and deviations from industry best practices.
Outcome
You’ll gain actionable insights to strengthen your defensive posture and mitigate risk to your infrastructure.
What you receive
Choosing a Security Configuration Review will give you a clear understanding of how attackers could exploit your infrastructure. You will get advice on how to prevent this from happening.
We create a comprehensive and actionable report, which includes:
A summary highlighting key risks
Technical findings across all reviewed systems
Risk prioritisation based on potential impact
Configuration improvement and guidance aligned with industry standards
Recommendations for improving long-term security
industries
Who we’ve helped
Our team has extensive experience across a wide range of industries, including:
Finance and Banking
Government and Public Sector
Healthcare and Pharmaceuticals
Transportation and Logistics
Retail and E-commerce
Education and Universities
Manufacturing and Industrial
IT and Software as a Service (Saas) Platforms
Utilities

What we assess
Our Security Configuration Reviews cover a broad range of enterprise technologies.
Employee devices are often the first point of entry for attackers. We review operating system policies, local administrator privileges, endpoint configurations, patch management and update policies, application control and execution policies, credential storage and authentication settings.
Servers host critical applications and sensitive data. This makes them high-value targets. We review operating system hardening, authentication and privilege management, secure remote administration configuration, patch and vulnerability management processes, logging and auditing configurations, backup and recovery settings.
Network infrastructure forms the backbone of enterprise connectivity and security.
We review firewalls and access control rules, network segmentation and VLAN configuration, router and switch security settings, secure management interfaces, logging and monitoring configurations, VPN and remote access security.
Cloud platforms introduce powerful capabilities but also complex security configurations.
We review Identity and Access Management (IAM) policies; storage security and data exposure risks; network security groups and firewall configurations; logging, monitoring, and audit configurations; privileged access and service account permissions, misconfigured cloud services and exposed endpoints.
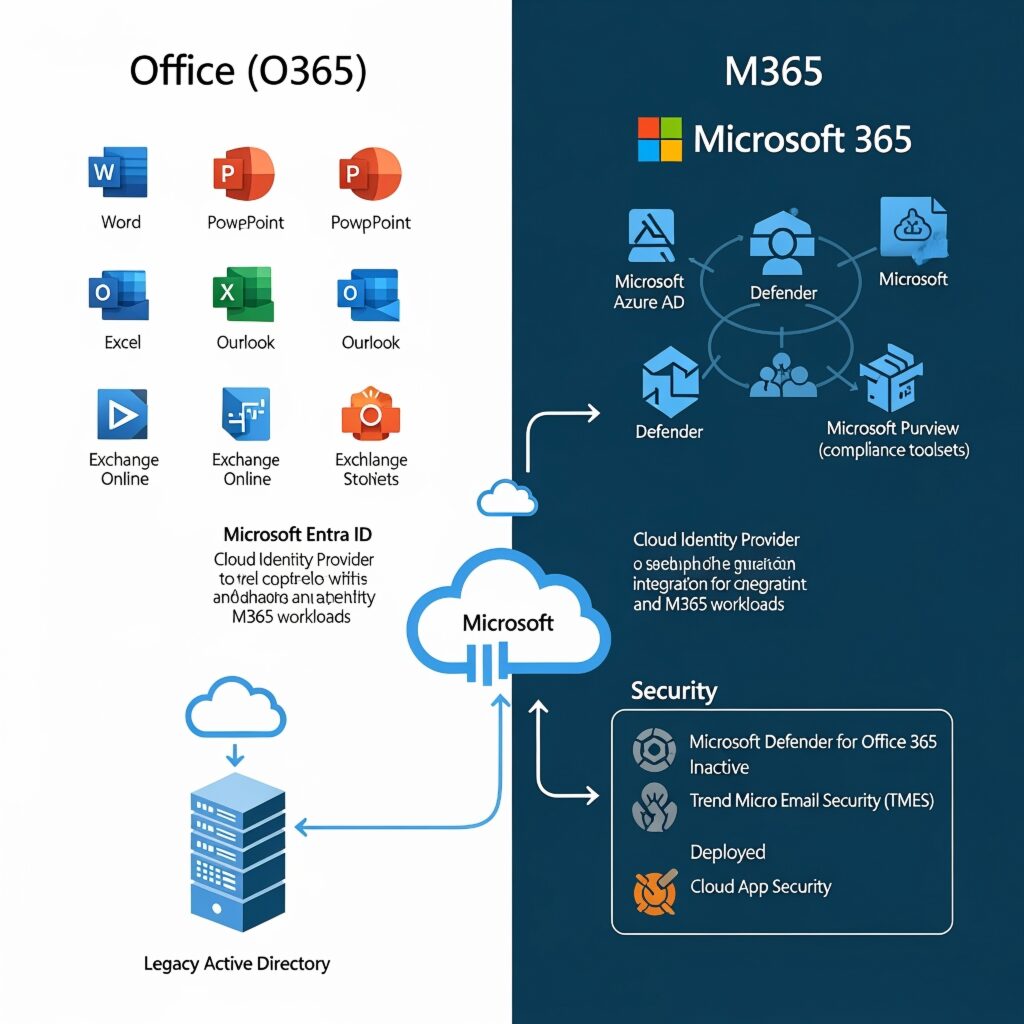
Many organisations rely on SaaS applications to run critical business processes. We review security configurations for platforms like Microsoft 365, CRMs, collaboration and communication tools, enterprise SaaS platforms used across business units.
Key areas include multi-factor authentication, access control and privilege management, conditional access policies, data sharing and external access settings, audit logging and monitoring configuration.
What frameworks we follow
Our methodology aligns with globally recognised security standards and best practices, including:
ISO/IEC 27001
NIST Cybersecurity Framework
CIS Critical Security Controls I
ASD Essential Eight
NZISM
These frameworks ensure your environment is evaluated against proven industry security practices.
FAQ
Find answers to common questions about our services and what to expect from your experience with us.
What systems can be included in a configuration review?
Configuration reviews can cover endpoints, servers, network devices, cloud platforms, identity systems, and SaaS platforms such as Microsoft 365.
How is this different from vulnerability scanning?
Vulnerability scanning identifies known software vulnerabilities, while configuration reviews evaluate how systems are configured and whether they follow security best practices.
Will changes be made to our systems during the review?
No. The assessment is read-only and focuses on identifying configuration weaknesses and hardening opportunities.
What standards are used during the review?
Assessments are typically aligned with recognised frameworks such as CIS Benchmarks, NIST guidance, and industry security best practices.
